Mirc 7.25 Registration Code Crackl ❲SAFE – 2025❳
Join the 4m players who have used the Aiming.Pro aim trainer to practice, train and improve their FPS aim skills
Start Aim TrainingJoin the 4m players who have used the Aiming.Pro aim trainer to practice, train and improve their FPS aim skills
Start Aim Training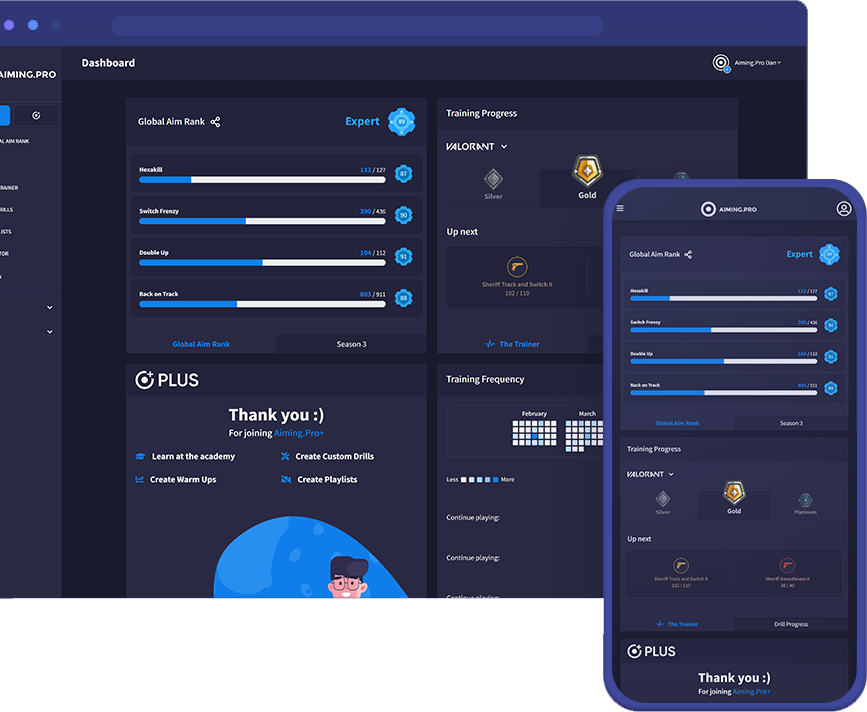
Software development is a resource-intensive process that involves significant investments in research, design, testing, and support. By not purchasing a legitimate license, users who rely on cracks deprive developers of the revenue needed to sustain their businesses and continue improving their software. This not only affects the developers but also the ecosystem of software development as a whole.
From a technical standpoint, using cracks to bypass registration codes can expose users to significant risks. Cracked software often originates from unverified sources, making it a potential vector for malware and other cyber threats. When users download and install cracked software, they may inadvertently compromise their systems' security, putting their personal data and sensitive information at risk. Mirc 7.25 Registration Code Crackl
In conclusion, while the temptation to use registration code cracks might be understandable, it's essential to consider the broader implications of such actions. The use of cracks not only deprives software developers of their rightful revenue but also exposes users to potential security risks. Instead of relying on cracks, individuals and businesses should explore legitimate alternatives, such as free trials, open-source software, or affordable subscription plans, to access the software they need. From a technical standpoint, using cracks to bypass
In the digital age, software has become an integral part of our daily lives. From operating systems to productivity tools, software enables us to perform a multitude of tasks efficiently. However, to use many software applications, users are required to obtain a registration code or license key, which often involves purchasing a subscription or a one-time license fee. The practice of using "cracks" to bypass these registration requirements has become a widespread phenomenon, raising significant ethical and technical concerns. In conclusion, while the temptation to use registration
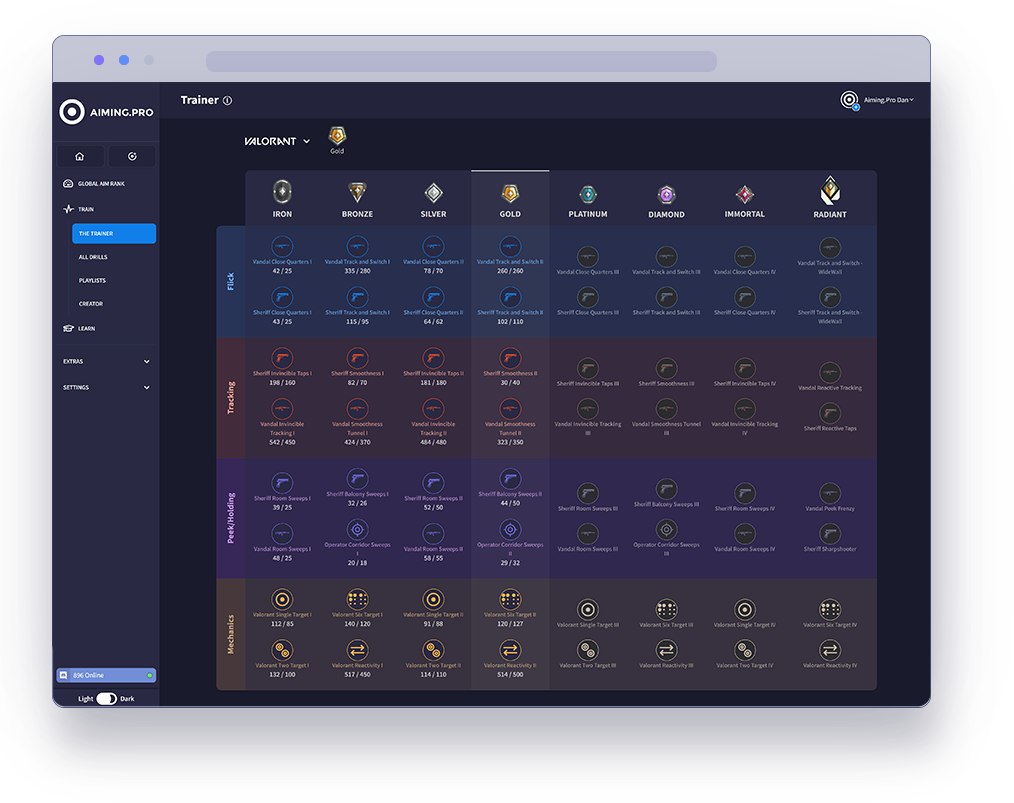
The Trainer is the best way to rank up in specific
FPS games using our aim trainer.
Our pros have analysed each game’s core concept
to carefully select drills that optimise your aim in the
areas that count. Hit the target goal in each level
and keep moving forwards to join the elite ranks of
Valorant, Apex, CSGO and COD.
Start your journey with The Trainer now
to unleash your full gaming potential.
See how you stack up against millions of players in our global community. Getting ranked lets you compete in our latest season of drills and weekly challenges.
Rank your aim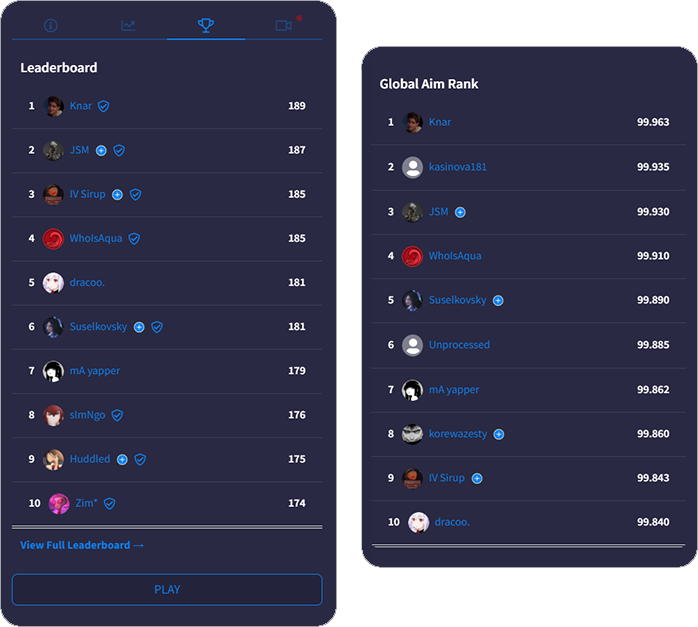
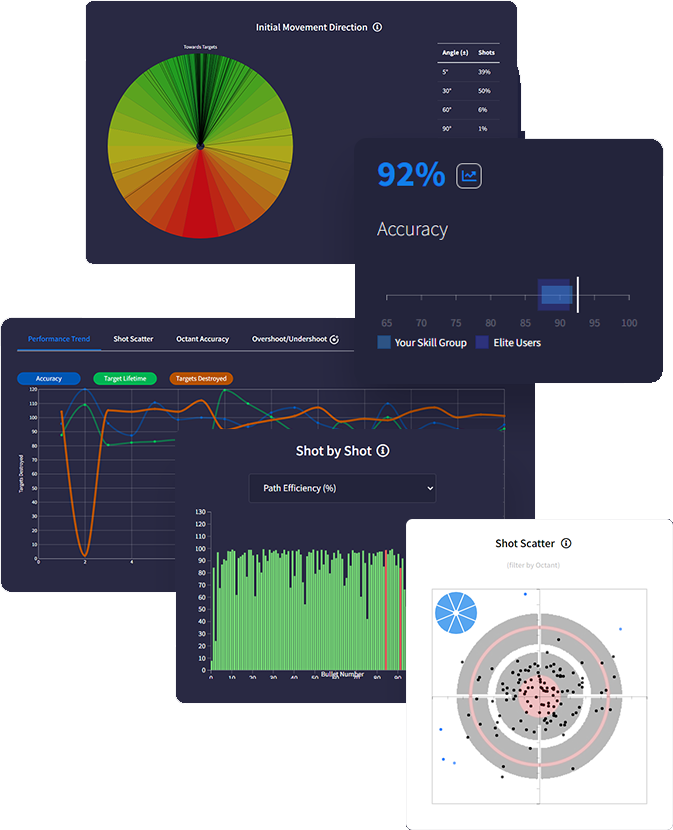
Get a deeper understanding of your performance with
with advanced data tracking. Discover insights that
uncover your strengths & weaknesses so you know
exactly how to optimise using actionable feedback.
Track everything after each drill with tons of metrics
measuring accuracy, reaction times, mouse speed,
move angles and more - the most in-depth analytics
ever built in an aim trainer.
Intelligently predict effective routines on evaluation of
your stats and trends. Analysing performance data
gives personalised feedback recommending skill areas for optimisation.
We support total synchronicity with all favourite FPS games. Our mouse sensitivity, FOV conversion, weapons and ADS variability accurately match real gaming physics ensuring all your aim gains translate into actual improved gameplay.
Sync sensitivity settings
to all FPS games

Adjust FOV to match
in-game preferences

Recreate ADS zoom &
sensitivity for every scope

Match weapon parameters
including rate of fire

Customise crosshair, hit
markers, textures & targets

Add your own sounds for
shots, hits, spawn & more
Software development is a resource-intensive process that involves significant investments in research, design, testing, and support. By not purchasing a legitimate license, users who rely on cracks deprive developers of the revenue needed to sustain their businesses and continue improving their software. This not only affects the developers but also the ecosystem of software development as a whole.
From a technical standpoint, using cracks to bypass registration codes can expose users to significant risks. Cracked software often originates from unverified sources, making it a potential vector for malware and other cyber threats. When users download and install cracked software, they may inadvertently compromise their systems' security, putting their personal data and sensitive information at risk.
In conclusion, while the temptation to use registration code cracks might be understandable, it's essential to consider the broader implications of such actions. The use of cracks not only deprives software developers of their rightful revenue but also exposes users to potential security risks. Instead of relying on cracks, individuals and businesses should explore legitimate alternatives, such as free trials, open-source software, or affordable subscription plans, to access the software they need.
In the digital age, software has become an integral part of our daily lives. From operating systems to productivity tools, software enables us to perform a multitude of tasks efficiently. However, to use many software applications, users are required to obtain a registration code or license key, which often involves purchasing a subscription or a one-time license fee. The practice of using "cracks" to bypass these registration requirements has become a widespread phenomenon, raising significant ethical and technical concerns.